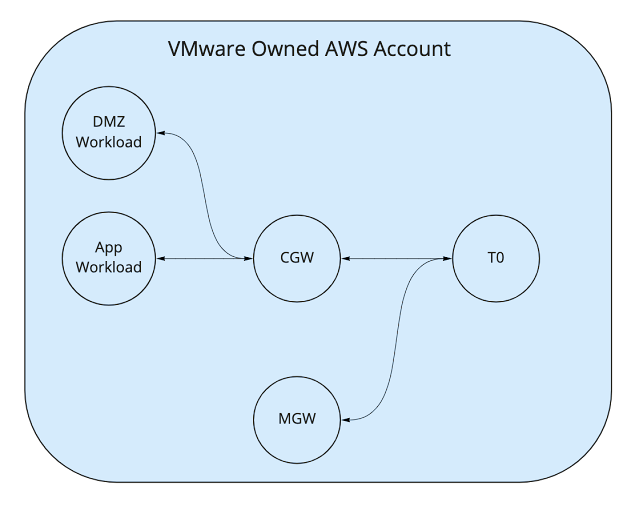
A colleague's customer recently had a requirement to host both DMZ and Production workloads in VMware Cloud on AWS while ensuring that traffic is segregated during transit. Currently, if the customer was to deploy DMZ and Production networks attached to the default Compute Gateway (CGW) Tier-1 then that traffic would be routed by the Tier-1 and thus violate the segregation required as per below:
Wednesday, 5 October 2022
VPN termination on a NAT'ed Tier-1 within VMware Cloud on AWS for DMZ traffic segregation
Friday, 11 February 2022
Registering VMware Cloud Disaster Recovery to vCenter with a restricted user account
A customer who is currently looking to deploy VMware Cloud Disaster Recovery (VCDR) globally recently asked about using a single active directory account with the minimum required permissions within vCenter as the account used to register their VCDR connectors to vCenter. For those who are new to VCDR, this is VMware's Disaster Recovery as a Service solution that offers on-demand disaster recovery with a very compelling total cost of ownership in comparison to on-premises.
The customer in question wanted to use a single active directory account across all their vCenters globally and didn't want to add the active directory
Wednesday, 9 February 2022
Routing to a connected VPC when attached to VMware Transit Connect
Recently there was an internal discussion around a customer request to access an Amazon FSx for Windows File Servers that was currently running in a connected VPC from another SDDC. The topology that the customer was looking at was as follows: